Overview
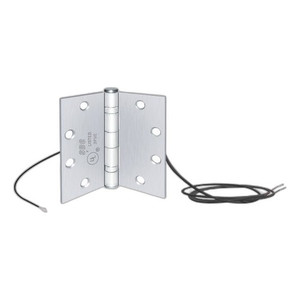
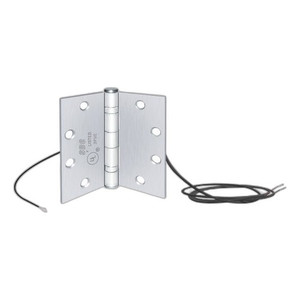
Sdc/Security Door Controls PTM-2AL 2-Wire Power Transfer
Sdc/Security Door Controls PTM-2AL 2-Wire Power Transfer Controller Overview The PTM-2AL is a 2-wire power transfer module designed to support multi-d…

Sdc/Security Door Controls PTM-2AL 2-Wire Power Transfer
Your recommended setup
Review items below — quantities update pricing automatically.
Bundle Summary
Overview
Sdc/Security Door Controls PTM-2AL 2-Wire Power Transfer Controller
Overview
The PTM-2AL is a 2-wire power transfer module designed to support multi-door access control deployments. This controller manages power distribution and communication across up to four doors, making it suitable for mid-scale access control installations in commercial and institutional environments.
Door Capacity & Credential Support
Supports 4-door capacity with HID credential compatibility. System accommodates up to 250,000 users, providing scalability for enterprise-level installations without requiring additional controller hardware.
Communication & Protocol
Features OSDP and TCP/IP communication protocols, enabling flexible network integration and interoperability with modern access control systems. Standard 18 AWG wiring configuration supports typical installation practices.
Installation Context
Ideal for security integrators deploying hardwired multi-door systems. Compatible with HID-based reader ecosystems and network-based access control platforms.
System Design, Deployment & Technical Support
Support services and planning resources for commercial surveillance, access control, and infrastructure deployments.
Fixed scope • Fixed price
System Design Assistance
- Get help validating product compatibility
- Coverage requirements
- Storage planning and deployment architecture before you buy.
Deployment & Configuration Support
- Access fixed-scope support for rollout planning
- User setup guidance
- Migration and system standardization across single-site or multi-site deployments
Guides, Tools & Calculators
- PoE requirements
- Storage retention
- Camera selection and deployment methodology